Trust Methods¶
Ideally, you’ve enabled and configured all of the product’s security mechanisms and are now ready to assign trust to elements in your workflows. Available trust mechanisms include:
Privileged locations¶
Privileged locations (PLs) are synonumous with “trusted locations.” PLs are the primary way that users and administrators can specify trusted content that should be exempt from security retrictions. The feature behaves as follows:
A privileged location may be a file, folder, or host.
There may be an HKCU list and an HKLM list: administrator’s can lock down the feature in HKLM so that users cannot change the setting.
Privileged locations can be permanently disabled or enabled by the administrator.
The Trust Manager hive does not appear in the registry until the user interface is exercised. However, you can create it manually.
Configuration may occur via the user interface or directly in the registry.
If configured through the user interface, the privileged location ID only may or may not appear under under all the possible cabs. Functionality changes across releases, so test the UI and see what trust is assigned.
Permissions granted by other features often overlap. For example, cross domain policies, internet access settings in Trust Manager, and certificate trust settings for certified documents sometimes interact so that the most permissive setting takes precedence. Users should TEST THEIR CONFIGURATION prior to deployment.
All key (tID) names under a particular cab must be unique.
You can also elevate Trusted Win OS zones to privileged locations.
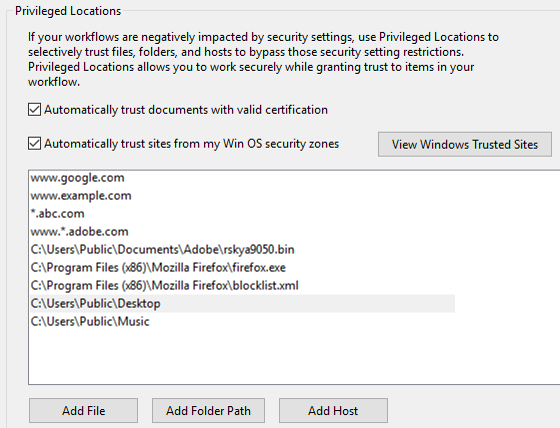
UI configuration¶
To specify a privileged location through the user interface:
Go to Preferences > Security (Enhanced).
Set a privileged location by selecting one of the following buttons:
Add File: A file is defined by a path, so its security settings will be invalid if that file is moved.
Add Folder Path: Prior to 10.1, trust is not recursive. With 10.1 and later, trust is recursive but can be disabled via a registry preference.
Add Host: Enter the root URL. You can use wildcards and do not have to enter any subdomain. For example,
www.adobe.combut notwww.adobe.com/lc. To specify HTTPS, select Secure Connections Only.
Choose OK.
Note
You cannot set a Temp directory as a privileged location as doing so presents a security risk.
Privileged locations
Wizard configuration¶
Admins can create privileged locations via the Wizard as well. However, keep in mind these locations are set under HKLM and they will not appear in the Privileged Location panel in the product. Adobe assumes that admin-created trust assigned to all users under HKLM should not be viewable or subject to end user changes.
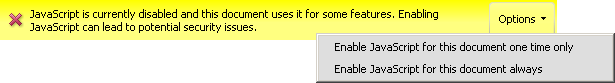
UI (on-the-fly) config.¶
Whenever a PDF opens that contains content which is blocked by a security feature, a Yellow Message Bar (YMB) appears. If the feature has not been disabled by the administrator, users can trust the document on-the-fly as follows:
When the YMB appears, choose Options.
Choose from one of the available trust options which vary by feature. Choosing Trust Always adds the current item to privileged locations.
YMB with trust options
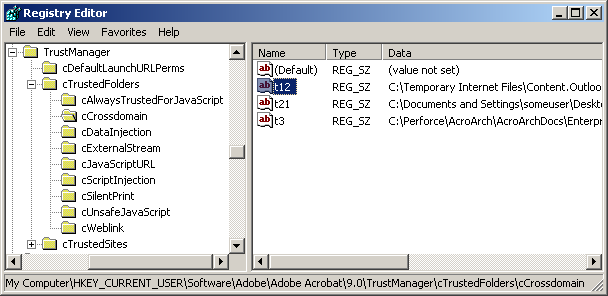
Registry configuration¶
The application stores information about privileged location trust in the registry and plist. Once a file is trusted via the UI or YMB, a t<unique id> is added to each of the cabs under cTrustedFolders|cTrustedSites. The container cab determines which restriction the document can bypass. For example, a tID under cCrossDomain allows cross domain access. For a complete list of available preferences see the Preference Reference.
While you can create PLs manually at the registry level, it’s easier to use the UI and then propagate those settings across your organization with the Wizard or post deployment via GPO or some other method. If you do decide to manually edit the registry, note the following:
TrustManager\cTrustedFolderscontains cabs for trusted folders AND files.TrustManager\cTrustedSitescontains cabs for trusted http and https hosts.Each t(ID) must be unique. In the example below, t3 could reside in each of the cabs, but there could not be more than one t3 in each cab.
[HKEY_CURRENT_USER\Software\Adobe\<product name>\<version>\TrustManager\cTrustedFolders\cCrossdomain]
"t3"="C:\\Documents and Settings\\username\\My Documents\\acrobat_logo16.png"
Protected View: trust set in the registry
Recursive directory trust¶
Recursivity is on by default with 10.1. Prior to 10.1, if you make a folder a privileged location its subdirectories are not automatically included. To make trust recursive, do the following:
Go to
HKEY_CURRENT_USER\Software\Adobe\<product name>\<version>\TrustManager\cTrustedFolders\.For each subkey (e.g. cCrossdomain) where trust should be recursive, go to the subkey.
For each folder ID that should be recursive, modify the name by appending _recursive to it.
Registry Configuration: Recursive trust
[HKEY_CURRENT_USER\Software\Adobe\<product name>\<version>\TrustManager\cTrustedFolders\cScriptInjection]
t5_recursive"="C:\\Aardvark"
Disabling Priv. Locations¶
You can disable and lock the ability to add privileged locations by setting the preferences as shown in the example below. This feature allows administrators to control what users can trust. Simply lock the feature and provide your own trust list to user machines. To do so, set the following:
Note
11.0 introduces support for locking on Macintosh.
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"bDisableTrustedFolders"=dword:00000001
"bDisableTrustedSites"=dword:00000001
Wildcard and host trust¶
10.x products support the use of wildcard matching of subdomain components for trusted host URLs. For example, for a basic URL of a.b.c.adobe.com, you can wildcard on all of a, b, or c. It is required that at least the first subdomain is specified (adobe in this case). So *.corp.adobe.com or lcforms.*.adobe.com works, but *.forms.corp.adobe.com or lcforms.corp.*.com will not.
Wild cards also work with IP addresses. For example, when https:// 153.39.154.100 or its wildcard combinations such as 153.39.154.* or 153.39.*.100 or 153.*.154.* are added to OS trusted locations, then the File opens outside PV.
Trusting IE trusted sites¶
You can also elevate Trusted Win OS zones to privileged locations since these are already under IT control. Prior to 10.1.2/9.5, bTrustOSTrustedSites provided trust for Trusted Sites. Beginning with 10.1.2 and 9.5, trust is also extended to Local Intranet Zones.
Note
Choosing Trust sites from my Win OS security zones extends trust to files when PV is set to Potentially unsafe locations. When PV is set to All Files, then OS trusted sites are not trusted and PDFs do not open outside of PV.
To make Internet Explorer’s trusted sites and zones behave as PLs:
Go to Preferences > Security (Enhanced).
Check Automatically trust sites from my Win OS security zones.
Choose OK. This options sets:
[HKEY_CURRENT_USER\Software\Adobe\<product name>\<version>\TrustManager]
"bTrustOSTrustedSites"=dword:00000001
Locking IE trusted sites¶
Windows OS trust can be locked so that users can’t change the setting via the UI as follows by setting bDisableOSTrustedSites as follows:
0: Disables trusting sites from IE and locks the feature.
1: Enables trusting sites from IE and locks the feature.
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"bDisableOSTrustedSites"=dword:00000000
Internet access¶
URLs can be blocked or allowed globally, or URL-specific settings can be created. See Internet access for details.
Certified document trust¶
11.0 introduces the ability to elevate any certified document to a privileged location for the Windows and Macintosh versions of Reader and Acrobat. When set, certified documents become trusted for exemption from the same security restrictions from which other privileged locations are exempt. Note the following:
The PDF’s certification signature must be valid and chain to a trusted root.
The setting is off by default.
The one exception to such trusted PDF’s parity with privileged locations is that this level of trust does not apply when the PDF is viewed in Protected View.
To enable this feature:
Choose Edit > Preferences (Windows) or (application name) > Preferences (Macintosh).
Select Security (Enhanced) in the Categories panel.
Check Automatically trust documents with valid certification. This sets:
[HKEY_CURRENT_USER\Software\Adobe\<product>\<version>\TrustManager]
"bTrustCertifiedDocuments"=dword:00000001
To lock the setting, set the following:
[HKLM\SOFTWARE\Policies\Adobe\<product>\<version>\FeatureLockDown\
"bEnableCertificateBasedTrust"=dword:00000001
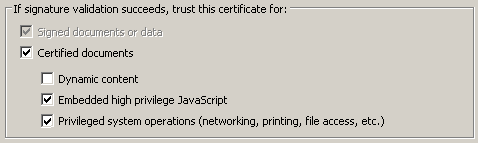
Per-certificate trust¶
Trust can be configured on a per-certificate basis so that certified documents signed with a specific certificate can be made exempt from some security restrictions. For the certification signature, the signature must be valid and the certificate must chain to a valid and trusted root certificate.
To set certificate trust:
Open Acrobat.
Do one of the following to open the Trusted Identities List:
9.x: Choose Security > Manage Trusted Identities and from the Display drop down list, choose Certificates.
10.x: Choose Tools > Sign and Certify > More Sign and Certify > Manage Trusted Identities and From the Display drop down list, choose Certificates.
11.x: Choose Edit > Preferences > Signatures > Identities and Trusted Certificates > More and select Trusted Certificates.
Select a certificate.
Choose Edit Trust.
Check one or more of the following.
Dynamic content: Enables multimedia. See Multimedia (legacy).
High privileged JavaScript: Enables HP JS execution. See High privileged JavaScript.
Privileged network operations: Enables those operations which are blocked when Enhanced Security is enabled. See Enhanced Security.
Choose Ok.
Certificate trust options
Cross domain trust¶
For details about setting up trust for cross domain access other than via privileged locations, see Cross Domain Configuration.
XObject (stream) access¶
Preference configuration can be a mystery if you don’t take to time to understand related features and how they interact. For example, enhanced security settings interact with certificate trust settings and Trust Manager settings. The following provides just one use case where two settings must be configured to get one feature to work as expected.
Since reference XObjects access external content, security is a concern. Therefore, XObject (external stream) access requires that such access be granted though the user interface (or registry) and that the referencing document is specified as trust-worthy when cross domain access is involved.
To configure XObject access:
To configure external content access:
Choose Edit > Preferences > Page Display (Windows) or Acrobat > Preferences Page Display (Macintosh).
Configure the Reference XObjects View Mode panel by setting Show reference XObject targets.
Set the location of referenced files (if any).
Choose OK.
Resource access
To configure trust via the registry:
Open the registry editor.
Go to
HKEY_CURRENT_USER\Software\Adobe\<product>\<version>\TrustManager\cTrustedFolders\cExternalStream.Right click and choose New String.
Enter a document ID in the form of t(some integer).
Right click on the new ID and choose Modify.
Enter the path to the trusted document in the Value Data field.
Go to
HKEY_CURRENT_USER\Software\Adobe\<product name>\<version>\TrustManager\cTrustedFolders\cCrossdomainand repeat the same steps. Use the same ID and value.
Note
Other XObject settings can be configured via the UI or in the registry as described in the Preference Reference for Acrobat and Adobe Reader.
EMF and XPS conversion to PDF¶
The December 2018 Acrobat release disabled XPS and EMF file conversion to PDF.
At Adobe, we build security into our products and we implement numerous security processes and controls to help us comply with industry-accepted standards, regulations and certifications. Some examples of overall security improvements specific to Acrobat and Reader include: sandboxing (Protected Mode and Protected View), fuzzing high value targets like the broker process, finding memory corruption bugs via ASAN/GFlags, and running continuous static analysis on the codebase. Additionally, as an added security measure, where we see features with low usage, like XPS and/or EMF to PDF conversion, we disable these features. However, if you trust the document origin, you can enable the feature by creating and setting the following preferences:
HKLM\SOFTWARE\(Wow6432Node)\Adobe\Adobe Acrobat\(track name)\FeatureState[BlockXPSParsing]=0
HKLM\SOFTWARE\(Wow6432Node)\Adobe\Adobe Acrobat\(track name)\FeatureState[BlockEMFParsing]=0