Security¶
The Security configuration panel helps configure the application security features such as enhanced security, protected mode, and privileged locations. Workflows and content should be designed to operate in the context of enabling all of these features; that is, untrusted content and source locations should be restricted, and trusted files, folders, and hosts should be specifically identified as privileged locations.
Note
Due to the complexity and critical nature of security settings, you might find it expedient to leverage existing configurations via the Registry feature. That is, configure an installed application and then copy the modified registry to the installer via the Wizard.
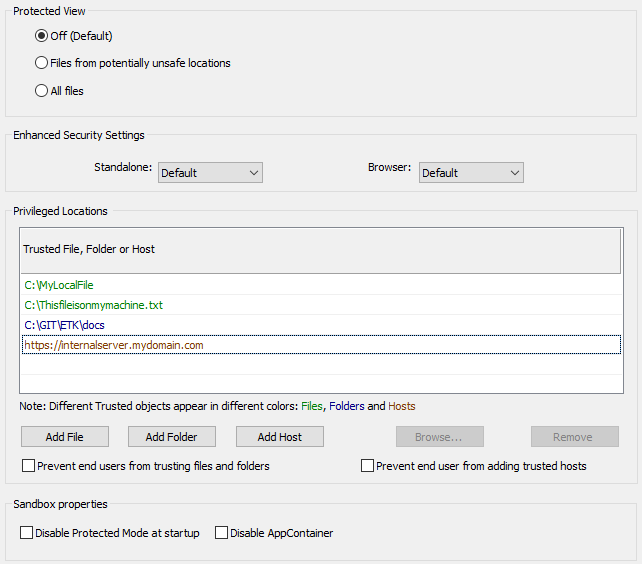
Security settings
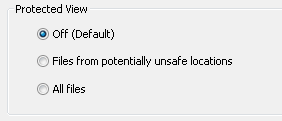
Protected View¶
Protected View (PV) is a highly secure “super-sandbox” that is essentially a read-only mode. In Protected View, all features are disabled except those associated with viewing, such as zoom, navigation, links, find, and more. Users must select Enable all features to do anything more than read the PDF. This action assigns trust and adds the document to the users’ list of Privileged Locations. PV behaves identically for Acrobat and Reader whether viewing PDFs in a browser or in a standalone product.
Note
In Reader 11.0, Protected View is only supported when Protected Mode is enabled. There can by no HKCU or HKLM Protected Mode registry preference set to 0 (off) when Protected View is enabled.
There are three configuration options:
Off: This default option disables the Protected View.
Files from potentially unsafe locations: Open files from the internet or other unknown (and therefore untrusted) sources in Protected View.
All files: Open all files in Protected View.
Protected View configuration
Enhanced security¶
Enhanced security configuration and behavior are similar across platforms, whether you are viewing a PDF within a browser or within a standalone application. Adobe recommends that you enable enhanced security. Enhanced security option restricts following behaviors and content:
Unrestricted cross domain access
Silent printing
XObject (stream) access
Data injection
Script injection
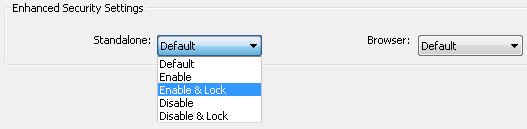
Standalone and browser behavior¶
Depending on how a PDF is opened, the PDF viewer may be a standalone application or may be opened within a browser. Settings may be configured separately for both cases. By default, enhanced security is enabled.
To specify a custom setting, set the Standalone and/or Browser drop down lists to one of the following:
Enable: Enhanced security is on but users can change the setting (the default).
Enable & Lock: Enhanced security is on but the UI is locked so that users can’t change the setting.
Disable: Enhanced security is off but users can change the setting.
Disable & Lock: Enhanced security is off but the UI is locked so that users can’t change the setting.
Disabling and enabling enhanced security toggles the keys shown below. Locking the setting sets a key in HKLM that’s only available to administrators.
Enhanced security configuration
Registry configuration: Enhanced security enabled
[HKCU\Software\Adobe\<product name>\<version>\TrustManager]
"bEnhancedSecurityInBrowser"=dword:00000001
"bEnhancedSecurityStandalone"=dword:00000001
Registry configuration: Locking enhanced security settings
[HKLM\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"bEnhancedSecurityStandalone"=dword:00000001
"bEnhancedSecurityInBrowser"=dword:00000001
[HKLM\SOFTWARE\Policies\Adobe\<product name>\<version>
\FeatureLockDown]
"bDisableTrustedFolders"=dword:00000001
"bDisableTrustedSites"=dword:00000001
Note
You may also want to lock this feature via HKLM’s FeatureLockDown: "bDisableOSTrustedSites"=dword:00000001.
Specify privileged locations¶
Privileged locations (PLs) are like “trusted locations” where the users and administrators can specify trusted content that should be exempt from security restrictions. The Wizard provides basic configuration options. However, registry configuration provides additional settings. The feature behaves as follows:
A privileged location may be a file, folder, or host.
There may be an HKCU list and an HKLM list: administrator’s can lock down the feature in HKLM so that users cannot change the setting.
Note
Admins can create privileged locations via the Wizard. However, the locations set under HKLM does not appear in the product’s Privileged Location panel. Adobe assumes that admin-created trust assigned to all users under HKLM should not be viewable or subject to end user changes.
Privileged locations can be permanently disabled or enabled by the administrator.
The Trust Manager hive does not appear in the registry until the user interface is exercised. However, you can create it manually.
Configuration may occur via the user interface or directly in the sregistry.
If configured through the user interface, the privileged location ID only may or may not appear under under all the possible cabs. Functionality changes across releases, so test the UI and see what trust is assigned.
Permissions granted by other features often overlap. For example, cross domain policies, internet access settings in Trust Manager, and certificate trust settings for certified documents sometimes interact so that the most permissive setting takes precedence. Users should TEST THEIR CONFIGURATION prior to deployment.
All key (tID) names under a particular cab must be unique.
You can also elevate Trusted Win OS zones to privileged locations.
To add a privileged location:
Choose Add File, Add Folder , or Add Host.
Enter a value or browse to the location.
Set whether trust should be recursive for folders and hosts (it is on by default).
The Wizard sets:
[HKLM\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"cTrustedFolder"
"cTrustedSites"
To remove a trusted object, select the trusted location and choose Remove.
Lock privileged locations¶
To determine whether end-users can add trusted objects, select or clear the following check boxes:
Prevent end-user to add trusted Files and Folders. This feature locks the user interface by setting:
[HKLM\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"bDisableTrustedFolders"=dword:00000001
Prevent end-user to add trusted Hosts. This feature locks the user interface by setting:
[HKLM\SOFTWARE\Policies\Adobe\<product name>\<version>\FeatureLockDown]
"bDisableTrustedSites"=dword:00000001